Fact-checked by the Snapmessages editorial team
Quick Answer
A SIM swap attack is a form of identity fraud where a criminal convinces your mobile carrier to transfer your phone number to a SIM card they control. As of May 2025, the FBI has reported losses exceeding $68 million annually from SIM swapping. Protect yourself by switching to app-based two-factor authentication and setting a carrier PIN.
A SIM swap attack — also called SIM hijacking or port-out fraud — occurs when a fraudster impersonates you to your mobile carrier and redirects your phone number to their own device. According to the FBI’s Internet Crime Complaint Center (IC3), SIM swapping complaints increased by more than 400% between 2018 and 2021, with financial losses rising sharply each year.
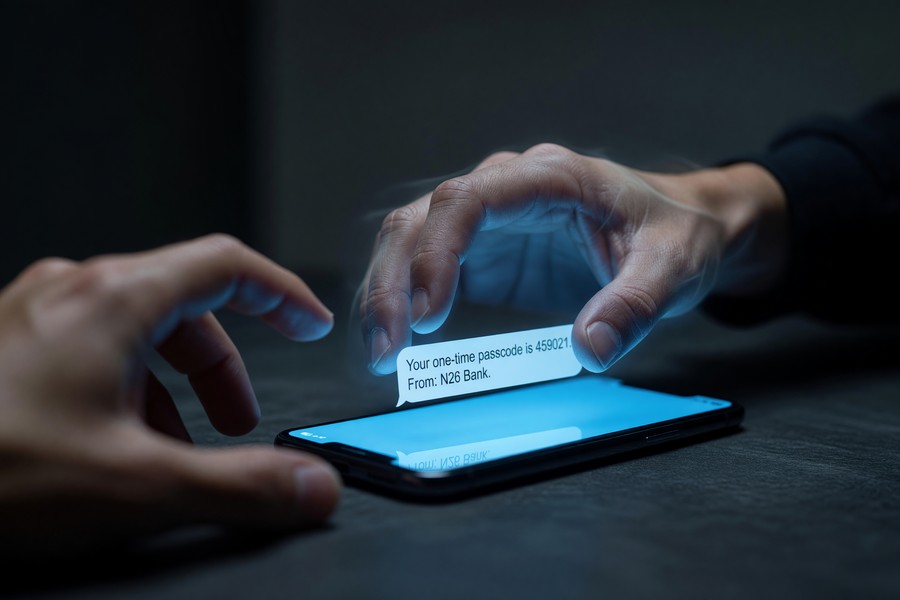
Once an attacker controls your number, they can intercept SMS-based one-time passwords and break into your bank accounts, email, and cryptocurrency wallets in minutes. This guide explains exactly how these attacks work, who is at risk, and the specific steps you can take right now to protect yourself.
Key Takeaways
- The FBI received 1,611 SIM swapping complaints in 2021 alone, with adjusted losses of more than $68 million (FBI IC3, 2022).
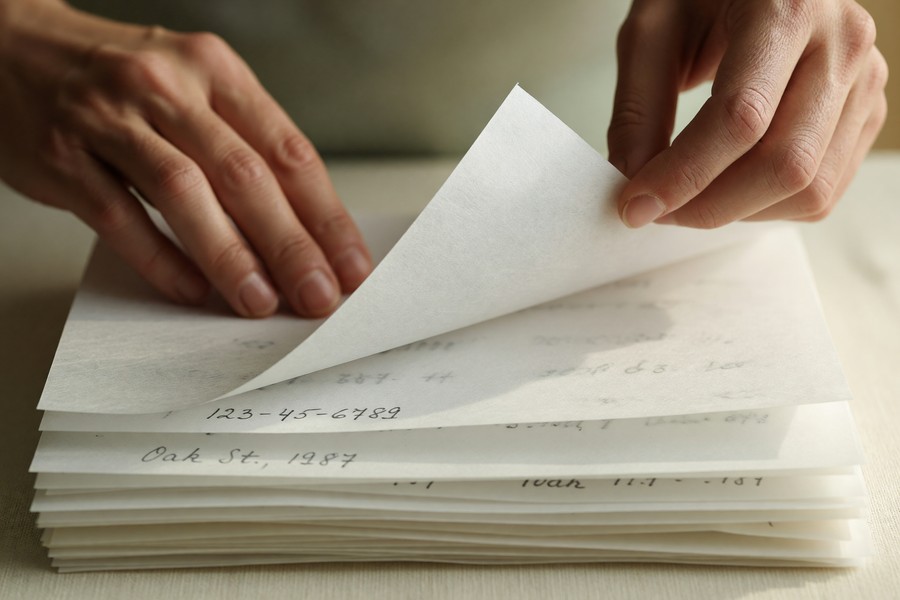
- Attackers typically need only 3–5 pieces of personal information — name, address, last four digits of SSN, and account PIN — to fool a carrier representative (FTC Consumer Information).
- SMS-based two-factor authentication is considered significantly weaker than app-based authenticators like Google Authenticator or Authy, because intercepted texts bypass the second factor entirely (NIST Special Publication 800-63B).
- The FCC adopted new rules in November 2023 requiring carriers to implement additional verification steps before completing a SIM swap or port-out request (FCC Consumer Guide).
- Cryptocurrency holders are disproportionately targeted — high-profile SIM swap cases have resulted in individual losses exceeding $20 million in a single incident (U.S. Department of Justice).
In This Guide
- How Does a SIM Swap Attack Actually Work?
- Who Is Most at Risk from SIM Swapping?
- What Are the Warning Signs of a SIM Swap Attack?
- How Can You Protect Yourself from a SIM Swap Attack?
- What Protections Do Mobile Carriers Offer?
- What Should You Do If You Are Already a Victim?
- Frequently Asked Questions
How Does a SIM Swap Attack Actually Work?
A SIM swap attack succeeds through social engineering — the attacker does not hack your phone directly. Instead, they call your carrier’s customer service line, claim to be you, and request that your number be moved to a new SIM card they already possess.
The attacker gathers your personal details beforehand, often through data breaches, phishing emails, or social media. With your name, address, and partial Social Security Number in hand, they can pass basic identity verification checks used by carriers like AT&T, Verizon, and T-Mobile.
The Step-by-Step Attack Process
The process unfolds in a predictable sequence that takes as little as 15 minutes from start to finish.
- The attacker collects your personal data via phishing, dark web purchases, or public records.
- They contact your carrier — by phone, online chat, or in person at a retail store — and impersonate you.
- They pass security verification and request a SIM swap to a device they control.
- Your phone loses signal immediately. The attacker now receives all calls and texts sent to your number.
- They use your phone number to reset passwords via SMS codes on your bank, email, and cryptocurrency accounts.
Carrier employees can be bribed directly. A U.S. Department of Justice indictment revealed that members of a SIM-swapping ring paid carrier insiders hundreds of dollars per swap to bypass verification entirely.
Why SMS Authentication Is the Weak Link
Most people rely on SMS text messages for two-factor authentication (2FA). Once an attacker controls your number, every SMS-based one-time password goes directly to them. Our guide on what two-factor authentication is and how it works explains why the method you choose for 2FA matters enormously.
NIST — the National Institute of Standards and Technology — officially deprecated SMS as a sole authentication factor in its SP 800-63B digital identity guidelines, citing the inherent vulnerabilities of the SS7 telephone network protocol that makes interception possible.
Who Is Most at Risk from SIM Swapping?
Anyone with a mobile phone number tied to a financial or email account is technically at risk, but certain groups face a dramatically elevated threat level. High-net-worth individuals, cryptocurrency holders, and public figures are the most frequently targeted.
Cryptocurrency investors are especially vulnerable because crypto transactions are irreversible. Once funds are transferred out of a wallet, they cannot be recovered. High-profile victims have included Twitter co-founder Jack Dorsey, whose account was hijacked in 2019 via a SIM swap, and multiple executives in the blockchain space.
Data Breaches Feed the Attack Pipeline
Attackers rarely work in a vacuum. They purchase stolen personal data from breaches involving companies like Equifax, T-Mobile, and Yahoo on dark web marketplaces. T-Mobile alone has disclosed multiple major data breaches affecting tens of millions of customers, each one expanding the pool of usable data for SIM swap attacks.
The average financial loss per SIM swapping victim in 2021 was approximately $42,206 — compared to just $4,848 for a typical phishing victim — according to FBI IC3 data.
| Target Profile | Primary Asset at Risk | Average Recovery Time |
|---|---|---|
| Cryptocurrency Investor | Crypto wallet, exchange accounts | Non-recoverable (irreversible transactions) |
| General Consumer | Bank accounts, email, social media | 3–14 days (with carrier and bank support) |
| Business Executive | Corporate accounts, sensitive communications | 7–21 days (legal and IT involvement required) |
| Social Media Influencer | Verified accounts, brand partnerships | 1–7 days (platform appeals vary widely) |
What Are the Warning Signs of a SIM Swap Attack?
The clearest sign of a SIM swap attack is sudden loss of cellular service — no calls, no texts, no mobile data — even though you are in an area with normal coverage. This happens because your number has already been transferred to the attacker’s SIM card.
Other warning signs appear quickly and should prompt immediate action. If you notice any of the following, treat it as an emergency and contact your carrier within minutes, not hours.
Immediate Red Flags to Watch For
- Your phone suddenly shows “No Service” or “SOS Only” unexpectedly.
- You receive unexpected texts or emails about account changes you did not initiate.
- You cannot log into accounts that previously worked fine.
- You receive calls from your carrier about a port or SIM change you did not request.
- Contacts report receiving strange messages from your number.
If you suspect your phone has been compromised beyond a SIM swap — including malware or spyware — our detailed guide on how to tell if your phone has been hacked covers the full range of indicators to check.
How Can You Protect Yourself from a SIM Swap Attack?
The single most effective defense against a SIM swap attack is removing SMS as your two-factor authentication method for all critical accounts. Replace it immediately with an authenticator app or a hardware security key.
Defense requires action at three levels: your mobile carrier, your online accounts, and your personal data hygiene. Each layer adds friction that makes a successful attack dramatically harder to execute.
Step 1 — Secure Your Carrier Account
Call your carrier — AT&T, Verizon, T-Mobile, or whichever provider you use — and set a unique, strong account PIN that is different from your standard passwords. Also request that a “port freeze” or “SIM lock” be placed on your account. This requires in-person verification at a store before any SIM change is approved.
Creating a strong, unique PIN starts with good password habits. Our guide on how to set a strong password you can actually remember provides a practical framework for creating credentials that are hard to guess but easy to recall.
Step 2 — Replace SMS-Based 2FA Immediately
Log into every important account — banking, email, social media, crypto exchanges — and switch 2FA from SMS to an authenticator app. Widely trusted options include Google Authenticator, Authy, and Microsoft Authenticator. For maximum security, a hardware key like a YubiKey from Yubico is the gold standard.
When switching away from SMS-based 2FA, prioritize these accounts first: primary email, online banking, and any platform that stores payment information. An attacker who controls your email can reset nearly every other account password within minutes.
Step 3 — Limit Your Digital Footprint
The personal details attackers need — date of birth, address, last four digits of your SSN — are often found on social media profiles or data broker websites. Review your privacy settings on Facebook, Instagram, and LinkedIn. Consider using a data removal service to scrub your information from public broker databases.
What Protections Do Mobile Carriers Offer?
All major U.S. carriers now offer voluntary account security features that directly reduce SIM swap risk, and new FCC regulations enacted in 2023 made stronger verification a legal requirement. Enabling these protections takes less than ten minutes but provides a significant barrier against attacks.
“SIM swapping is one of the most underreported forms of identity theft. Consumers have more power than they realize — a single call to set a port freeze with your carrier can block the majority of these attacks before they start.”
Carrier-Specific Security Features
AT&T offers “Extra Security,” which requires a passcode before any account changes. Verizon provides a “Number Lock” feature accessible through its app. T-Mobile has implemented “SIM Protection,” which must be manually enabled in your account settings. All three carriers now require additional verification before processing a SIM swap under the FCC’s updated consumer protection rules.
It is also worth understanding how newer messaging protocols interact with your phone number’s security. Our explainer on the difference between SMS and RCS covers how these protocols transmit your messages and why the underlying network matters for security.
What Should You Do If You Are Already a Victim?
If you believe a SIM swap attack is in progress, call your carrier immediately using a different phone — a landline, a family member’s phone, or a VoIP line. Request an emergency SIM swap reversal and place a port freeze on your account. Speed is critical: every minute of delay gives the attacker more time to access accounts.
After regaining control of your number, follow these steps in order to contain the damage.
Immediate Recovery Actions
- Contact your carrier and confirm your number is restored to your SIM.
- Change passwords on all important accounts, starting with your primary email.
- Notify your bank immediately — request that no transactions be processed for 24 hours if possible.
- File a complaint with the FTC at ReportFraud.ftc.gov and with the FBI’s IC3 at IC3.gov.
- Check your credit reports at AnnualCreditReport.com and consider placing a fraud alert with Experian, TransUnion, and Equifax.
- Enable all available 2FA options on every account using an authenticator app, not SMS.
You can place a free credit freeze with all three major bureaus — Experian, Equifax, and TransUnion — which prevents new credit accounts from being opened in your name, even if an attacker holds your personal information. The Consumer Financial Protection Bureau (CFPB) recommends this as a baseline identity protection measure for all consumers.
Understanding the broader landscape of digital privacy — including what metadata your communications reveal — is also part of protecting yourself long-term. Our guide on what message metadata is and who can see it explains what information can be exposed even when message content is encrypted.
Frequently Asked Questions
Can a SIM swap attack happen without my knowledge?
Yes. In most cases, victims have no warning until their phone loses service. The entire transfer can be completed by a carrier representative in under five minutes, often outside business hours when customer support is handled by staff with less verification oversight.
Is there a difference between a SIM swap and a port-out scam?
They are closely related but technically distinct. A SIM swap moves your number to a new SIM card on the same carrier. A port-out scam transfers your number to a completely different carrier. Both result in the attacker receiving your calls and texts, but port-out scams can be harder to reverse quickly.
Does using end-to-end encrypted messaging protect against SIM swapping?
End-to-end encryption protects message content in transit, but it does not prevent a SIM swap. If an attacker controls your phone number, they can receive new SMS verification codes sent by any service. Switching to encrypted messaging apps for sensitive conversations reduces exposure, but carrier-level protections are still essential.
Are prepaid carrier users at higher risk?
Prepaid accounts have historically had weaker identity verification requirements than postpaid accounts, making them a more common target for SIM swapping. The FCC’s 2023 rules apply to all carriers and account types, which has improved protections somewhat, but the risk gap has not been fully closed.
Can two-factor authentication via an authenticator app be bypassed by a SIM swap?
No. Authenticator apps generate time-based codes locally on your device and do not depend on your phone number or cellular connection. An attacker who has swapped your SIM cannot receive or intercept codes generated by Google Authenticator, Authy, or a hardware key like a YubiKey.
What legal recourse do victims have?
Victims can file complaints with the FTC, FBI IC3, and their state attorney general’s office. Civil lawsuits against carriers have succeeded in some high-profile cases. In 2021, a California court awarded $75.8 million to a victim who successfully sued AT&T for failing to prevent a SIM swap that resulted in cryptocurrency theft.
How long does it take to recover from a SIM swap attack?
Restoring your phone number typically takes one to four hours with carrier assistance. Recovering compromised accounts, disputing fraudulent transactions, and restoring full security across all platforms typically takes three to fourteen days depending on the number of accounts affected and the speed of institutional responses.
Sources
- FBI Internet Crime Complaint Center (IC3) — 2022 SIM Swapping Public Service Announcement
- FCC — SIM Swapping and Port-Out Scam Consumer Guide
- FTC Consumer Information — Phone Number Port-Out Scams
- NIST Special Publication 800-63B — Digital Identity Guidelines: Authentication and Lifecycle Management
- U.S. Department of Justice — Eight Individuals Charged in Nationwide SIM Hijacking Scheme
- Consumer Financial Protection Bureau (CFPB) — Credit Reports and Scores
- FTC — ReportFraud.ftc.gov (Official Fraud Reporting Portal)
- AnnualCreditReport.com — Free Official Credit Report Access
- T-Mobile — Additional Information Regarding 2021 Cyberattack
- FBI Internet Crime Complaint Center (IC3) — Official Complaint Portal







